KEY POINTS
Claude Mythos Preview scored 93.9% on SWE-bench and found thousands of critical vulnerabilities in every major OS and web browser, but Anthropic is refusing to release it publicly.
Project Glasswing partners include AWS, Apple, Cisco, CrowdStrike, Google, JPMorganChase, Microsoft, NVIDIA, and Palo Alto Networks — a rare tech-security alliance worth watching.
Experts warn that adversaries already have AI and that the window between a vulnerability's discovery and its exploitation has been compressed to minutes.
TOP STORY
An AI So Capable, Even Anthropic Won't Set It Loose

Here's a useful way to think about this. Imagine hiring a security auditor so sharp they can scan your entire office building in minutes, flag every faulty lock, every cracked window, every exposed wire — and hand you a list before anyone else even knocks on the door. That's roughly what Claude Mythos Preview can do. Except the "building" is digital infrastructure used by billions of people, and the "list" contains thousands of high-severity vulnerabilities hiding in every major operating system and web browser on the planet.
Anthropic's new model scored 93.9% on SWE-bench Verified and 83.1% on CyberGym — benchmarks that measure a model's ability to understand code and find exploitable weaknesses. In plain terms, it is extraordinarily good at doing what hackers do, but faster and at scale.
That's the breakthrough. And that's also the problem. A tool that finds vulnerabilities can just as easily be used to exploit them. So instead of a public release, Anthropic launched Project Glasswing — a structured, invitation-only deployment designed to put this capability to work for defense, not offense.
Why the Name Glasswing?
The glasswing butterfly is transparent — you can see right through its wings. The name signals Anthropic's stated intent: total visibility, nothing hidden. The project is designed to be open with partner organizations about what the model finds, even when the findings are uncomfortable.
The partner roster reads like a who's who of the tech world: Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, The Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks. That's not a press release list. That's a coordinated response to a real and urgent problem.
WHY IT MATTERS TO YOU
The Clock Was Already Running Before Mythos Arrived

Here's what most people miss when they read about Project Glasswing: the "good guys getting a head start" framing assumes the race hasn't already started. It has.
Bradley Smith, SVP and Deputy CISO at BeyondTrust, made this crystal clear. His team has already seen AI-assisted tooling compress the exploitation window for critical vulnerabilities to minutes, not weeks. That was before Mythos. That was with the tools already in circulation.
⚠️ Security Alert
BeyondTrust's Smith put it plainly: "This is not a technology problem with a technology solution." Finding more bugs faster doesn't automatically fix them. The bottleneck is organizational will, funding, and speed of response — none of which an AI model changes on its own.
For investors in cybersecurity names, this creates a real dynamic worth tracking. More vulnerabilities discovered faster means more contracts for companies like CrowdStrike and Palo Alto Networks. But it also raises the bar for what those companies need to deliver.
Marcus Fowler, CEO of Darktrace Federal, adds a layer that most headlines skipped entirely: as traditional entry points get patched, attackers pivot. They stop trying to break through windows and start looking for people who already have keys. Insider threats, compromised credentials, coerced employees — those risks go up as perimeter defenses go up.
THE BIG PICTURE
What the Experts Are Actually Saying
The security community's reaction has been cautiously positive — but nobody's celebrating yet. Here's a quick tour of the expert consensus.
John Gallagher of Viakoo Labs raised what may be the most alarming point of all: while IT systems run on a handful of major operating systems, there are over 150,000 operating systems used in OT, IoT, and critical physical systems — factories, water treatment plants, access control panels. There is no "Windows Update" for a water pump. Mythos will likely find a tsunami of zero-day vulnerabilities in these systems, and most organizations have zero infrastructure in place to patch them.
💡 Expert Perspective
Morey Haber of BeyondTrust flagged four downstream consequences worth watching: a flood of newly discovered zero-days, contractual disclosure obligations triggering private notifications before fixes are ready, unstructured patch backlogs for on-premise systems, and Anthropic itself gaining training exposure to a wide range of commercial code it wouldn't otherwise access.
Jason Schmitt of Black Duck offered the most grounded take: "It is not difficult to find something that matters. It's extremely difficult to find everything that matters." False negatives — vulnerabilities the model misses — are more dangerous than false positives. No model eliminates that risk. Defense in depth still matters.
Diana Kelley of Noma Security cut straight to the organizational response. Her first priority for security teams: assume discovery will accelerate whether you want it to or not, and build faster validation pipelines now. Her second: take a hard look at your legacy vulnerability backlog. Exceptions that were once accepted as "low risk" because exploitation was hard may not be low risk anymore.
Ram Varadarajan of Acalvio may have the most sobering data point of all: less than 1% of the vulnerabilities Mythos found have actually been fixed. That gap is not a technology problem. It's a capacity and prioritization problem. And attackers with similar AI tools can find those same holes independently.
BY THE NUMBERS
The Data Behind the Headlines
93.9% — Claude Mythos score on SWE-bench Verified, measuring code understanding and bug-finding ability
83.1% — Mythos score on CyberGym, a cybersecurity-specific evaluation benchmark
Thousands of high-severity vulnerabilities already found across every major OS and web browser
<1% of those vulnerabilities have been patched, according to Acalvio's CEO
150,000+ operating systems in use across OT, IoT, and industrial control systems, vs. a handful in traditional IT
11 partners signed onto Glasswing: AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, The Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks
Minutes — the current exploitation window for critical CVEs, according to BeyondTrust, down from weeks just a year ago
CVSS 9.0+ — the score threshold that triggers contractual disclosure obligations for many enterprise software agreements
MARKET SNAPSHOT
Project Glasswing Partners
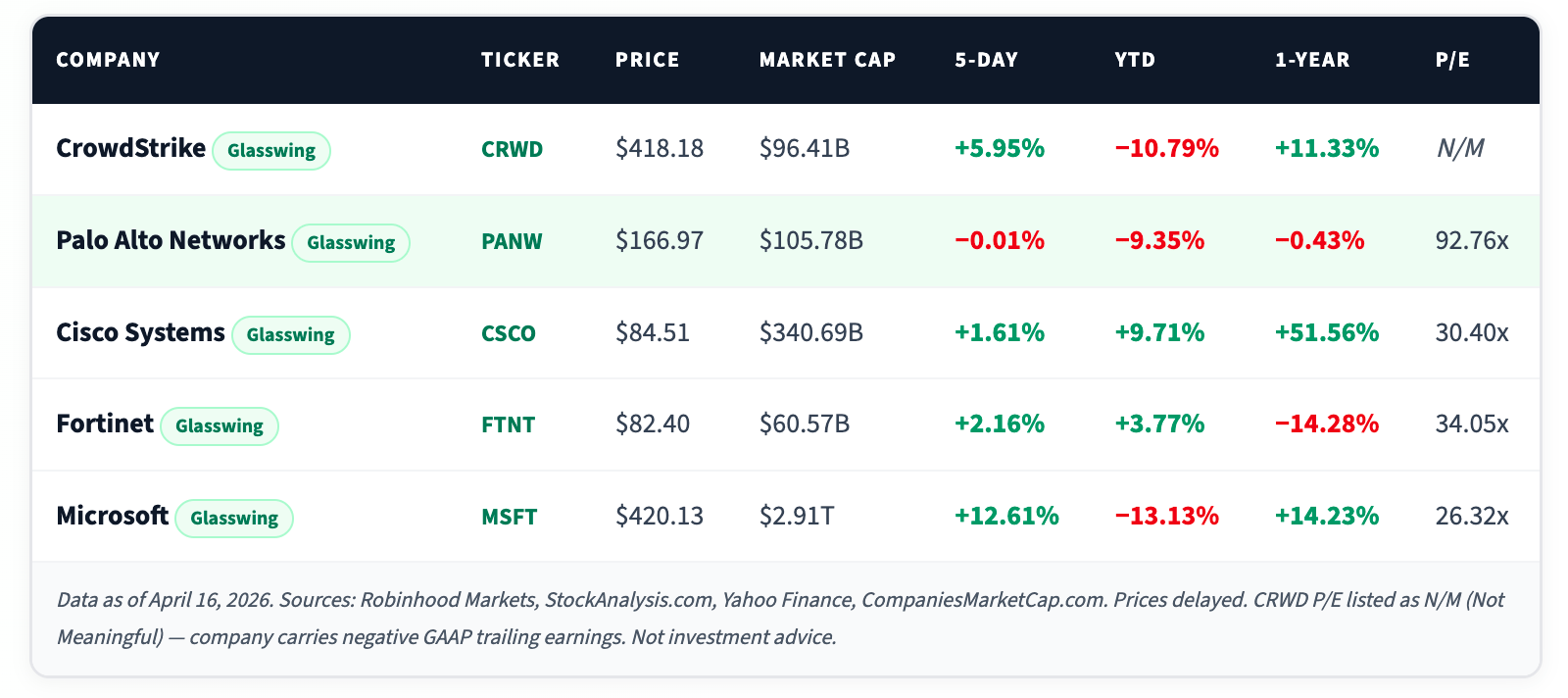
Five of the eleven Glasswing partners are publicly traded. Here's where they stand as of April 16, 2026 — and how the market has responded in the week following the announcement.
WHAT TO WATCH
Three Things That Will Define This Story
Patch Velocity
Right now, fewer than 1% of discovered Mythos vulnerabilities have been fixed. Watch whether Glasswing partners publicly disclose remediation timelines. Speed of patching is the real metric — not discovery.
OT / IoT Exposure
Viakoo's Gallagher flagged over 150,000 operating systems in industrial and IoT environments — with no update infrastructure. Any Glasswing expansion into this space would be a major catalyst for specialized security vendors.
Regulatory Response
CVSS 9.0+ findings trigger contractual disclosure obligations. A flood of new critical CVEs could force a wave of private notifications before fixes exist — and invite Congressional scrutiny of AI-driven vulnerability discovery.
THE BOTTOM LINE
Claude Mythos and Project Glasswing represent something genuinely new: an AI so capable at finding security weaknesses that its creators chose controlled deployment over a public release.
The security community broadly supports the direction — but nobody's relaxed. Adversaries already have AI. The exploitation window is down to minutes.
OT and IoT systems are dangerously exposed. Legacy vulnerability backlogs need urgent review.
No single model replaces the need for layered, continuously monitored, human-aware security architecture.
Glasswing isn't the finish line. It's the starting pistol.



